The Quick Brief
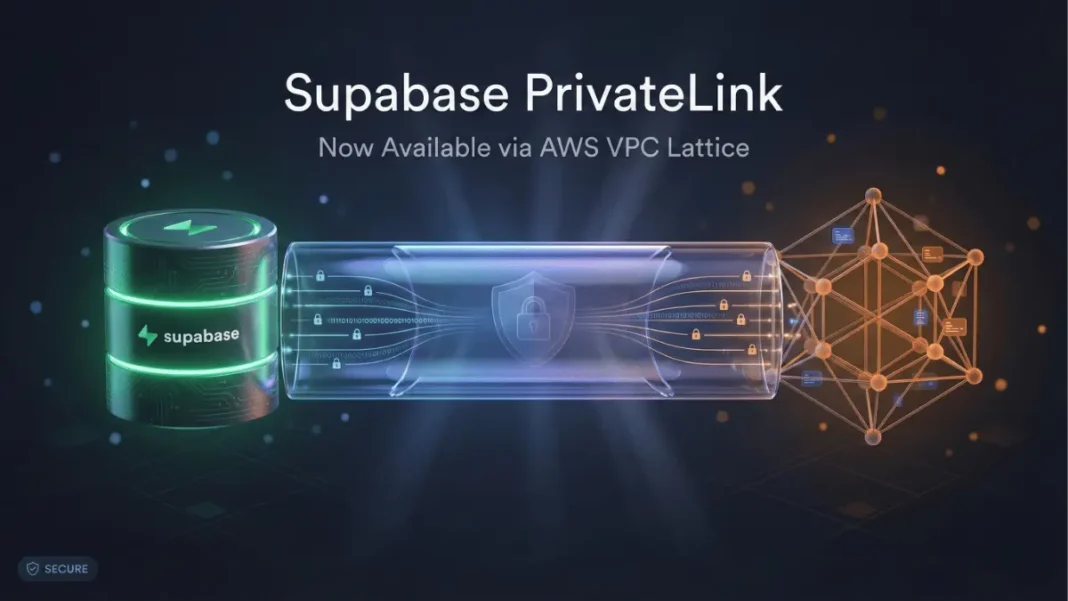
- The Launch: Supabase deployed PrivateLink on January 27, 2026, using AWS VPC Lattice to enable private network connectivity between AWS VPCs and Supabase databases.
- The Impact: Team and Enterprise customers can route database traffic exclusively through AWS private network, eliminating public internet exposure.
- The Context: Beta release supports only direct database and PgBouncer connections; API, Storage, Auth, and Realtime services continue over public internet.
Supabase announced PrivateLink availability on January 27, 2026, bringing private network connectivity to its backend-as-a-service platform. The infrastructure leverages AWS VPC Lattice to establish secure database connections that bypass the public internet entirely.
AWS VPC Lattice Architecture Powers Private Connectivity
The implementation operates as an organization-level configuration, utilizing VPC Lattice Resource Configurations shared across multiple AWS accounts for each Supabase project. Each resource share follows the naming format sspl-[project_ref]-[random alphanumeric string].
Database traffic flows through private AWS infrastructure exclusively. Connectivity requires accepting the VPC Lattice Resource Configuration in AWS Resource Access Manager, then configuring security groups to permit traffic on port 5432 (TCP). Organizations can use PrivateLink endpoints or VPC Lattice Service Networks for establishing connections.
Current beta limitations restrict PrivateLink to direct database and PgBouncer connections only. Supabase services including API, Storage, Auth, and Realtime continue operating over public internet connections during this phase. Read replicas are not supported in the beta release.
AdwaitX Analysis: Network Isolation for Regulated Industries
Network isolation provides enhanced security posture by minimizing attack surface through elimination of public internet exposure. The architecture addresses data governance requirements without application code modifications.
Organizations can disable public-facing connectivity entirely after migrating applications to private endpoints. Connection string updates transition applications from public endpoints (db.[project-ref].supabase.co) to private VPC endpoints (your-private-endpoint.vpce.amazonaws.com).
Technical Specifications
| Component | Details |
|---|---|
| Technology | AWS VPC Lattice |
| Availability | Beta – Team and Enterprise plans |
| Supported Services | Direct database, PgBouncer connections |
| Excluded Services | API, Storage, Auth, Realtime |
| Port | TCP 5432 (Postgres) |
| Requirements | AWS VPC in same region as Supabase project |
| Regional Exception | eu-central-2 (Zurich) – Expected April 2026 |
| Read Replicas | Not supported in beta |
| Resource Share Format | sspl-[project_ref]-[random alphanumeric] |
Implementation Process and Configuration
Setup requires AWS account ID registration through the Supabase dashboard’s Integrations section under organization settings. After registration, users must accept the VPC Lattice Resource Configuration in AWS Resource Access Manager.
Security group configuration must permit inbound traffic on port 5432 with destination rules appropriate for application subnet or security group topology. Applications require connection string updates to migrate from public endpoints to private VPC endpoints, with thorough connectivity testing recommended before disabling public access.
Organizations requiring public connectivity disablement must contact Supabase support to ensure all monitoring and backup tools transition to private endpoints. The eu-central-2 (Zurich) region will receive PrivateLink support in April 2026.
The beta phase enables Supabase to refine the offering based on enterprise customer feedback. Read replica support and additional service coverage remain under development as the company expands PrivateLink capabilities beyond core database connections.
Frequently Asked Questions (FAQs)
What is Supabase PrivateLink?
PrivateLink uses AWS VPC Lattice to route database connections through private AWS infrastructure, eliminating public internet exposure.
How does Supabase PrivateLink improve database security?
It provides network isolation within AWS infrastructure, reducing attack surface and enabling complete disablement of public database access.
Which Supabase plans support PrivateLink?
PrivateLink is available in beta exclusively to Team and Enterprise subscription customers.
Does Supabase PrivateLink work with all Supabase services?
No. Beta supports only direct database and PgBouncer connections. API, Storage, Auth, and Realtime continue using public internet.
When will PrivateLink be available in Zurich (eu-central-2)?
Expected availability is April 2026.