Summary: CVE-2025-55182 (React2Shell) is a critical remote code execution vulnerability affecting React Server Components with a maximum CVSS score of 10.0. The flaw allows unauthenticated attackers to execute arbitrary code through malicious HTTP requests targeting default configurations. React 19.x and Next.js 15.x/16.x are vulnerable, with exploitation observed in the wild since December 5, 2025. Immediate patching to React 19.0.1+, 19.1.2+, or 19.2.1+ and corresponding Next.js versions is required. Alibaba Cloud offers Security Center scanning, WAF virtual patches, and Cloud Firewall blocking to protect affected applications.
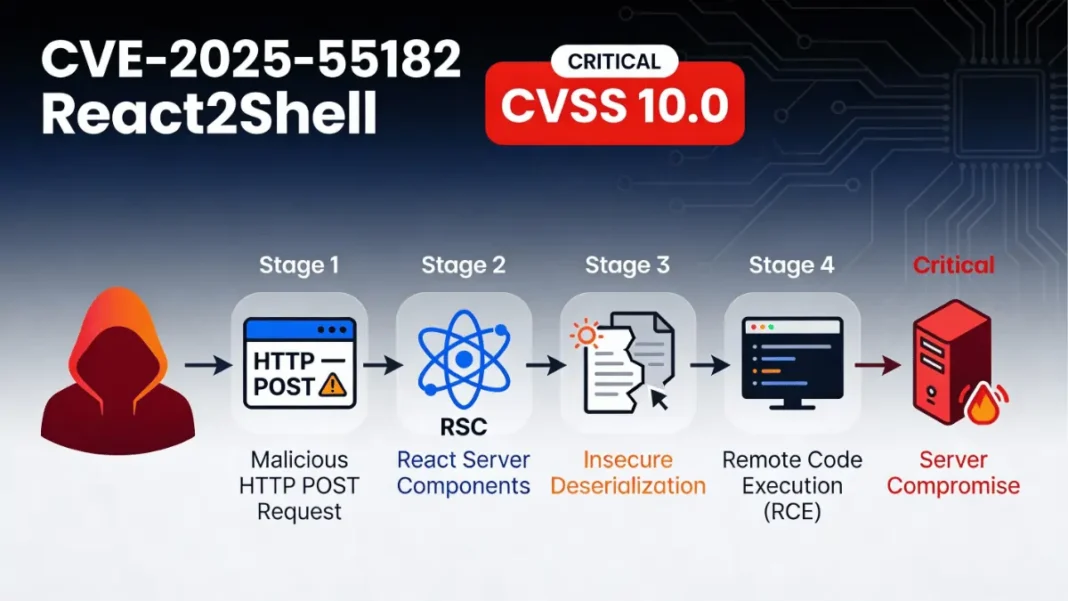
On December 3, 2025, the React team disclosed CVE-2025-55182, a critical remote code execution vulnerability affecting React Server Components. With a perfect CVSS score of 10.0, this flaw allows unauthenticated attackers to compromise servers running affected versions of React and Next.js. Within hours of public disclosure, multiple state-sponsored threat groups began actively exploiting the vulnerability. This guide provides technical analysis, detection methods, and step-by-step remediation instructions including Alibaba Cloud’s protection strategy.
What Is CVE-2025-55182?
CVE-2025-55182, nicknamed “React2Shell,” is an unauthenticated remote code execution vulnerability in React Server Components’ Flight protocol. The flaw affects applications using React 19.x and frameworks that implement RSC, most notably Next.js 15.x and 16.x.
The vulnerability exists in default configurations, meaning standard Next.js apps created with create-next-app are exploitable without any code changes . Attackers need only craft a malicious HTTP request to the target server to achieve code execution.
CVE-2025-55182 is a critical deserialization flaw in React Server Components that enables unauthenticated remote code execution with a CVSS score of 10.0, affecting default configurations of React 19.x and Next.js 15.x/16.x applications.
Technical Breakdown
The vulnerability stems from insecure deserialization in RSC payload handling logic. When React Server Functions receive specially crafted payloads from clients, the server fails to properly validate the data structure . This allows attacker-controlled input to influence server-side execution, ultimately running arbitrary JavaScript code with server privileges.
Unlike typical RCE vulnerabilities requiring authentication or specific misconfigurations, CVE-2025-55182 exploits a fundamental flaw in how React processes client requests. Even applications that don’t explicitly implement Server Functions remain vulnerable if they support React Server Components.
Why It Earned a 10.0 CVSS Score
The maximum severity rating reflects four critical factors:
- No authentication required: Attackers can exploit the flaw remotely without credentials
- Default configuration vulnerable: No special setup needed by developers
- High exploitation reliability: Proof-of-concept exploits demonstrate near-100% success rates
- Widespread deployment: Next.js powers millions of production applications globally
According to Wiz Research, 39% of cloud environments contain vulnerable React or Next.js instances, with 44% of all cloud environments running publicly exposed Next.js applications .
Which Frameworks and Versions Are Affected?
React Vulnerable Versions
All releases of these packages in versions 19.0.0, 19.1.0, 19.1.1, and 19.2.0 are vulnerable:
react-server-dom-webpackreact-server-dom-parcelreact-server-dom-turbopack
Patched versions include 19.0.1, 19.1.2, and 19.2.1.
Next.js Vulnerable Versions
Next.js versions affected include:
- 14.3.0-canary.77 and later canary releases (downgrade to 14.x stable recommended)
- All 15.x releases prior to patched versions
- All 16.x releases prior to patched versions
Other Affected Frameworks
Any framework bundling React Server Components implementation is potentially vulnerable, including:
- React Router (unstable RSC APIs)
- Waku
- Vite RSC plugin (
@vitejs/plugin-rsc) - Parcel RSC plugin (
@parcel/rsc) - Redwood SDK (
rwsdk) - Expo (with RSC support)
Vulnerable versions include React 19.0.0–19.2.0, Next.js 14.3.0-canary.77+, 15.x, and 16.x, plus frameworks like React Router, Waku, Vite RSC, Parcel RSC, and Redwood SDK that implement React Server Components.
Real-World Exploitation Timeline
China-Nexus Threat Groups Observed
Amazon Web Services threat intelligence detected active exploitation attempts within hours of CVE-2025-55182’s December 3 public disclosure. Multiple China state-nexus threat groups, including Earth Lamia and Jackpot Panda, began weaponizing the vulnerability on December 4, 2025.
AWS noted that threat actors experimented with early public exploit code before researchers released fully functional proof-of-concept tools.
Cryptomining Campaigns Detected
Wiz Research identified the first confirmed victim compromises starting December 5, 2025, at 6:00 AM UTC . Attackers primarily targeted internet-facing Next.js applications and Kubernetes containers.
Post-exploitation activity included :
- Credential harvesting from environment variables and AWS instance metadata
- Installation of Sliver malware framework for persistent access
- Deployment of XMRig cryptominers (both UPX-packed and standard versions)
- Base64 encoding of AWS credentials for exfiltration
GreyNoise reported 95 unique IP addresses conducting automated exploitation attempts beginning December 5 at 04:00 UTC .
How to Check If Your Application Is Vulnerable
Manual Version Check
Inspect your package.json dependencies:
json{
"dependencies": {
"react": "19.x.x", // Check version
"react-dom": "19.x.x",
"next": "15.x.x" // Next.js version
}
}
If React is 19.0.0, 19.1.0, 19.1.1, or 19.2.0, you’re vulnerable. For Next.js, check against the affected version list above.
Automated Scanning with Security Tools
Run these commands to audit dependencies:
bashnpm audit
# or
yarn audit
# or
pnpm audit
Look for CVE-2025-55182 in vulnerability reports.
Alibaba Cloud Security Center Detection
Alibaba Cloud customers can leverage Security Center’s automated scanning:
- Enable Security Center in your Alibaba Cloud console
- Navigate to Vulnerabilities → Application Vulnerability
- Use Host Protection → Agentless Detection to scan ECS instances without installing agents
- Review detected CVE-2025-55182 instances and prioritize remediation
The agentless detection feature performs security assessments with negligible performance impact.
Check if you’re vulnerable by inspecting package.json for React 19.0.0–19.2.0 or Next.js 15.x/16.x versions, running npm audit, or using Alibaba Cloud Security Center’s agentless vulnerability scanner to automatically detect CVE-2025-55182 across ECS hosts.
Step-by-Step Patching Guide
Patching Next.js Applications
Run the appropriate command for your current Next.js version:
bash# For Next.js 13.3.x–14.x
npm install next@14.2.35
# For Next.js 15.0.x
npm install next@15.0.7
# For Next.js 15.1.x
npm install next@15.1.11
# For Next.js 15.2.x
npm install next@15.2.8
# For Next.js 15.3.x
npm install next@15.3.8
# For Next.js 15.4.x
npm install next@15.4.10
# For Next.js 15.5.x
npm install next@15.5.9
# For Next.js 16.0.x
npm install next@16.0.10
If you’re on Next.js 14.3.0-canary.77 or later canary, downgrade to stable 14.x:
bashnpm install next@14
Patching React Server Components
For applications using React Server Components directly:
bashnpm install react@latest react-dom@latest
npm install react-server-dom-webpack@latest
# or for other bundlers
npm install react-server-dom-parcel@latest
npm install react-server-dom-turbopack@latest
Framework-specific updates:
React Router:
bashnpm install react@latest react-dom@latest react-server-dom-webpack@latest @vitejs/plugin-rsc@latest
Waku:
bashnpm install react@latest react-dom@latest react-server-dom-webpack@latest waku@latest
Redwood SDK:
bashnpm install rwsdk@latest
npm install react@latest react-dom@latest react-server-dom-webpack@latest
Verifying the Update
After patching, confirm versions in package.json and package-lock.json:
bashnpm list react react-dom next
Rebuild your application:
bashnpm run build
Deploy the patched version immediately to production environments.
Alibaba Cloud Protection Strategy
Alibaba Cloud Security provides multi-layered defense against CVE-2025-55182 exploitation.
Security Center Vulnerability Scanning
Asset Identification automatically discovers applications using affected React or Next.js versions across your ECS fleet. The platform provides:
- Real-time vulnerability detection via Application Vulnerability module
- Agentless scanning with zero performance impact
- Remediation guidance with precise upgrade recommendations
- Risk prioritization based on exposure and exploitability
WAF Virtual Patching
Alibaba Cloud Web Application Firewall deploys virtual patches to block CVE-2025-55182 exploitation attempts at the network edge. Virtual patches provide immediate protection while you complete application updates, filtering malicious RSC payloads before they reach vulnerable servers.
Cloud Firewall Real-Time Blocking
Cloud Firewall integrates with threat intelligence feeds to block known malicious IP addresses conducting exploitation campaigns. The service provides:
- 7×24 continuous security monitoring
- Automatic rule updates based on emerging threat data
- Protection against zero-day exploitation windows
Emergency Response Services
For customers who suspect active compromise, Alibaba Cloud Security offers:
- Emergency incident response with rapid intervention
- Root cause analysis and forensic investigation
- Immediate remediation assistance
- Post-incident risk assessment reports
- Security posture hardening recommendations
Featured Snippet Box: Alibaba Cloud protects against CVE-2025-55182 through Security Center agentless scanning, WAF virtual patches that block exploitation attempts, Cloud Firewall real-time IP blocking, and 24/7 emergency response services for incident investigation and remediation.
Temporary Mitigation Options
If immediate patching isn’t feasible, implement these stopgap measures:
Custom WAF Rules
Configure Web Application Firewall rules to detect and block malicious RSC payloads. Look for:
- Unusual content types in POST requests to RSC endpoints
- Malformed serialization patterns in request bodies
- Suspicious encoding schemes in flight protocol data
Note that WAF rules provide partial protection only determined attackers may bypass signature-based detection.
Network-Level Blocking
Restrict access to React Server Function endpoints:
- Implement IP allowlisting for trusted client ranges
- Require VPN or internal network access for administrative functions
- Deploy rate limiting to slow automated exploitation attempts
Monitoring for IOCs
Watch for indicators of compromise :
- DNS queries to OAST testing domains (
*.oast.live,*.oastify.com) - Unexpected child processes spawned by Node.js/Next.js
- Outbound connections to cryptomining pools
- AWS credential access patterns in CloudTrail logs
- Base64-encoded data in unusual network traffic
Technical Deep Dive: How the Exploit Works
Insecure Deserialization Explained
React Server Components use a serialization format called “Flight” to transmit data between client and server. When a client invokes a Server Function, React serializes the function call and arguments into a Flight payload transmitted via HTTP POST .
The server deserializes this payload to reconstruct the function call. CVE-2025-55182 exploits insufficient validation during deserialization. Attackers craft malicious Flight payloads containing references to internal Node.js modules (like child_process) that shouldn’t be accessible from client input .
When the vulnerable React Server Components code deserializes the payload, it evaluates the attacker-controlled module references, instantiating objects that execute arbitrary code.
Attack Vector Analysis
A typical exploit follows this sequence:
- Attacker identifies a React Server Components endpoint (usually
/_next/data/in Next.js) - Attacker crafts a malicious Flight-formatted payload containing dangerous module references
- Payload is sent via HTTP POST to the Server Function endpoint
- Vulnerable React Server Components code deserializes the payload without proper validation
- Attacker-controlled code executes with Node.js process privileges
- Attacker establishes reverse shell, harvests credentials, or installs persistence mechanisms
The attack requires no authentication and works against default configurations. Exploitation reliability approaches 100% in testing environments .
The Bottom Line
CVE-2025-55182 represents one of the most critical vulnerabilities in modern web frameworks, with widespread exploitation already underway. The combination of a perfect 10.0 CVSS score, default-vulnerable configurations, and publicly available exploits makes immediate patching non-negotiable.
Immediate action steps:
- Audit all React and Next.js applications for vulnerable versions
- Apply patches using the version-specific commands in this guide
- Deploy WAF rules and monitoring for exploitation indicators
- Review security logs for compromise evidence from December 5 onward
For Alibaba Cloud customers: Enable Security Center’s agentless vulnerability scanning and leverage WAF virtual patches for comprehensive protection.
Vulnerable vs. Patched Versions
Here’s the vulnerability table in the same style as your laptop comparison table:| Package | Vulnerable Versions | Patched Versions | Patch Date |
|---|---|---|---|
| react-server-dom-webpack | 19.0.0, 19.1.0, 19.1.1, 19.2.0 | 19.0.1, 19.1.2, 19.2.1+ | Dec 3, 2025 |
| react-server-dom-parcel | 19.0.0, 19.1.0, 19.1.1, 19.2.0 | 19.0.1, 19.1.2, 19.2.1+ | Dec 3, 2025 |
| Next.js | 14.3.0-canary.77+, 15.x, 16.x | 14.2.35, 15.0.7+, 16.0.10+ | Dec 3, 2025 |
| React Router RSC | All unstable RSC API versions | Latest with React 19.0.1+ | Dec 3, 2025 |
| Waku | Versions with React 19.0–19.2 | Latest with React 19.0.1+ | Dec 3, 2025 |
CVE Severity Comparison
| CVE ID | Vulnerability Type | CVSS Score | Authentication Required | Exploitation Difficulty | Public Exploits |
|---|---|---|---|---|---|
| CVE-2025-55182 | Remote Code Execution | 10.0 | No | Low | Yes |
| CVE-2025-66478 (duplicate) | Remote Code Execution | 10.0 | No | Low | Yes |
| CVE-2025-55184 | Denial of Service | 7.5 | No | Low | Yes |
| CVE-2025-55183 | Source Code Exposure | 5.3 | No | Medium | Yes |
| CVE-2025-67779 | Denial of Service | 7.5 | No | Low | Yes |
Protection Methods Comparison
| Protection Method | Implementation Speed | Effectiveness | Maintenance Required | Cost |
|---|---|---|---|---|
| Patching to Fixed Versions | 1–2 hours | 100% | Low | Free |
| Alibaba Cloud WAF Virtual Patch | < 10 minutes | 95% | Medium | Paid service |
| Custom WAF Rules | 30–60 minutes | 70% | High | Variable |
| Network IP Allowlisting | 15–30 minutes | 60% | Medium | Free |
| Cloud Firewall Blocking | < 10 minutes | 85% | Low | Paid service |
| Protection Method | Implementation Speed | Effectiveness | Maintenance Required | Cost |
| Patching to Fixed Versions | 1–2 hours | 100% | Low | Free |
| Alibaba Cloud WAF Virtual Patch | < 10 minutes | 95% | Medium | Paid service |
| Custom WAF Rules | 30–60 minutes | 70% | High | Variable |
| Network IP Allowlisting | 15–30 minutes | 60% | Medium | Free |
| Cloud Firewall Blocking | < 10 minutes | 85% | Low | Paid service |
Frequently Asked Questions (FAQs)
What makes CVE-2025-55182 so dangerous compared to other vulnerabilities?
CVE-2025-55182 achieves maximum severity because it requires no authentication, exploits default configurations, has near-100% exploitation reliability, and affects millions of production applications. Unlike most critical vulnerabilities requiring specific misconfigurations, React2Shell impacts standard deployments created with official tooling .
How can I tell if my Next.js application was already compromised?
Check server logs for unusual POST requests to /_next/data/ endpoints between December 4–5, 2025 . Look for DNS queries to *.oast.live or *.oastify.com, unexpected child processes spawned by Node.js, outbound connections to known cryptomining pools, and AWS CloudTrail logs showing unusual metadata service access.
Does updating React automatically fix Next.js applications?
No, Next.js bundles its own React version. You must update Next.js itself using the version-specific commands provided in the patching guide. Simply updating React in package.json won’t protect Next.js applications.
Can I use Alibaba Cloud WAF to protect non-Alibaba Cloud applications?
Alibaba Cloud WAF primarily protects applications hosted on Alibaba Cloud infrastructure. For applications on other platforms, consider equivalent WAF solutions from your hosting provider or implement custom protection rules.
What’s the difference between CVE-2025-55182 and CVE-2025-66478?
CVE-2025-66478 was initially assigned to the Next.js manifestation of the vulnerability but has since been rejected as a duplicate of CVE-2025-55182 . Both reference the same underlying flaw in React Server Components Next.js was vulnerable because it uses the affected React packages.
Are React 18 applications vulnerable to CVE-2025-55182?
No, React 18 doesn’t include React Server Components, which were introduced in React 19. Traditional client-side-rendered React applications using React 18 or earlier are not affected by this vulnerability.
How quickly can attackers exploit CVE-2025-55182 after discovering a vulnerable server?
Exploitation takes seconds using automated tools . Public proof-of-concept exploits can scan and compromise vulnerable servers with a single crafted HTTP request. GreyNoise detected 95 IP addresses conducting automated exploitation campaigns within 24 hours of exploit publication.
Will Alibaba Cloud automatically patch my applications?
No, Alibaba Cloud provides detection, virtual patches (temporary WAF-based protection), and monitoring, but you must manually apply application-level patches. Virtual patches block exploitation attempts while you complete the upgrade process.
Featured Snippet Boxes
What is CVE-2025-55182:
CVE-2025-55182 is a critical deserialization flaw in React Server Components that enables unauthenticated remote code execution with a CVSS score of 10.0, affecting default configurations of React 19.x and Next.js 15.x/16.x applications.
Affected Versions:
Vulnerable versions include React 19.0.0–19.2.0, Next.js 14.3.0-canary.77+, 15.x, and 16.x, plus frameworks like React Router, Waku, Vite RSC, Parcel RSC, and Redwood SDK that implement React Server Components.
How to Check Vulnerability:
Check if you’re vulnerable by inspecting package.json for React 19.0.0–19.2.0 or Next.js 15.x/16.x versions, running npm audit, or using Alibaba Cloud Security Center’s agentless vulnerability scanner to automatically detect CVE-2025-55182 across ECS hosts.
Alibaba Cloud Protection:
Alibaba Cloud protects against CVE-2025-55182 through Security Center agentless scanning, WAF virtual patches that block exploitation attempts, Cloud Firewall real-time IP blocking, and 24/7 emergency response services for incident investigation and remediation.
Patching Priority:
CVE-2025-55182 requires immediate patching due to its 10.0 CVSS score, active exploitation since December 5, 2025 by state-sponsored groups, publicly available exploits, and vulnerability in default configurations affecting 39% of cloud environments.
Exploitation Timeline:
China-nexus threat groups including Earth Lamia and Jackpot Panda began exploiting CVE-2025-55182 on December 4, 2025, with widespread automated attacks and cryptomining campaigns detected starting December 5 at 6:00 AM UTC.